Using Azure Automation to Invite Entra ID B2B Users
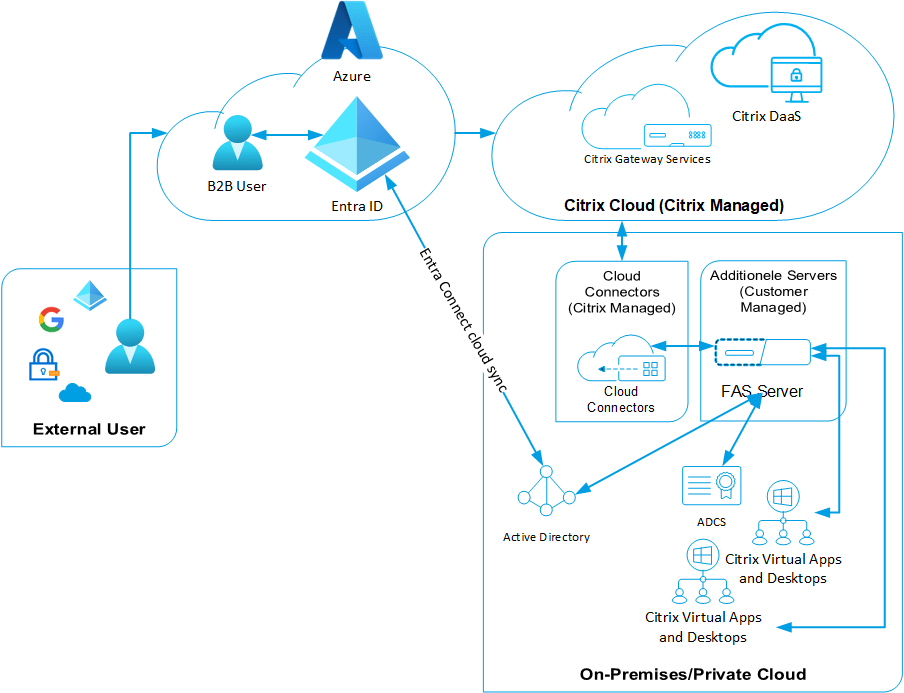
In a previous article about using Entra ID B2B users, I needed to set up some user extensions. In that article, I also mentioned that many customers needed to access the environment, which meant that multiple users needed to be changed.As this is an ongoing business and we like to